springer white papers on security testing metrics|security metrics review pdf : service Continuous Testing, Security as Code, Threat modelling, Risk analysis, Monitoring and logging and Red Team security drills. Continuous Testing is the practice of having automatic security controls throughout the software development lifecycle, continuously detecting for defects in code changes with the possibility of automatic rollback if . WEB1 de jul. de 2018 · A song for the playful girl of Baldi's basics in education and learning.Spotify: https://open.spotify.com/album/5Xtlhs2yENoQ3o4dunNfdMApple .
{plog:ftitle_list}
webDescarregue mais de 79,693 ícones de alvo em formato SVG, PSD, PNG, EPS ou como webfonts. Flaticon, a maior base de dados de ícones gratuitos.
Standards and certification are among the most effective responses to ensure an adequate level of trust. This paper demonstrates that metrics and measurements play a . Metrics provide decision support in running an organization. When an organization establishes a set of metrics, the organization can get a realistic baseline, or view, of how it . Then, basics and recent developments of security testing techniques applied during the secure software development lifecycle, i.e., model-based security testing, code-based testing and static . Continuous Testing, Security as Code, Threat modelling, Risk analysis, Monitoring and logging and Red Team security drills. Continuous Testing is the practice of having automatic security controls throughout the software development lifecycle, continuously detecting for defects in code changes with the possibility of automatic rollback if .
Software Quality refers to two related but distinct notions: 1. Software functional quality reflects how well it complies with or conforms to a given design based on functional requirements or specifications. Footnote 2 That attribute can also be described as the fitness for the purpose of a piece of software or how it compares to competitors in the marketplace as a .
This paper describes the framework for security measurement method and shows how it is used for information security assurance in Estonia. . They emphasis that systematic and complete security metrics are needed in the decision-making process. . RCIS 2022. Lecture Notes in Business Information Processing, vol 446. Springer, Cham. https .
Agile software development methods being relatively new and quite in its developmental stages, need the design of correlating metrics is since the traditional metrics may not suffice. This paper focuses on proposing some metrics that can measure the progress and quality of a product being developed using Agile software development methods with .Handschuh, H.: Contactless Technology Security Issues. Security Technologies Department, Gemplus. Information Security Bulletin 9, 95 (2004) Google Scholar Schneidewind, N.F.: Methodology for validating software metrics. IEEE Software Engineering 18, 410–422 (1992) Article Google Scholar
This paper explores how reliability analysis and cyber-security analysis can be combined using Artificial Intelligence and Machine Learning (AI/ML), and Large Language Models (LLM) to produce a . The Green Grid: The Green Grid Productivity Indicator. Technical report, White Paper #15, The Green Grid (2008) Google Scholar The Green Grid: ERE: a Metric for Measuring the Benefit of Reuse Energy from a Data Center. Technical report, White Paper #29, The Green Grid (2010) Google ScholarTo encourage more work in this direction, this paper explores the motivation behind the ongoing adoption of a service paradigm and provides a set of metrics that could be beneficially investigated by academia to help businesses address more effectively the need for both service provider and consumer to have Security Assurance.
Fuzzing is an important technique in software and security testing that involves continuously generating a large number of test cases against target programs to discover unexpected behaviors such as bugs, crashes, and vulnerabilities. Recently, fuzzing has advanced considerably owing to the emergence of new methods and corresponding tools. However, it . For security organizations, metrics are a way to regularly monitor how well security controls, the security organization, and the organization as a whole are performing relative to security goals. In fact, ISACA’s CISM Review Manual suggests: “Key controls that cannot be monitored pose an unacceptable risk and should be avoided” [p 194, 3]. A. A. Abdulrazeg et al. (2012) have developed security metrics to improve misuse case model for discovering and fixing defects and vulnerabilities. The proposed security metrics indicates the possibility of security defects. The metrics have been developed using goal question metric approach (GQM). The presented metrics consist of two main goals. Detecting security vulnerabilities in the source code of software systems is one of the most important challenges in the field of software security. We need an effective solution to discover and patch vulnerabilities before our valuable information is compromised. Security testing is a type of software testing that checks whether software is vulnerable to cyber .
An Introduction to Journal Metrics. Speed, usage, and impact make-up the suite of Springer journal metrics. Browse the sections below to learn what the calculated metrics can tell you about the performance of your journal article and journal. . Source Normalized Impact per Paper (SNIP) measures contextual citation impact by weighting . Penetration testing textbooks advise their readers to follow a pre-established methodology. For example, Johansen et al. write: “A penetration testing methodology defines a roadmap, with practical ideas and proven practices that can be followed to assess the true security posture of a network, application, system, or any combination thereof” [].
The convergence of product and enterprise IT poses entirely new cybersecurity risks, from compromised functional safety to data privacy. The automotive industry is using various methods for security verification and validation, but with classic security testing vulnerability detection is inefficient and incomplete.
This paper makes the following contributions in the context of microservices: Proposal of three metrics (Microservice endpoint coverage, Test case endpoint coverage, and Complete Test suite endpoint coverage) to assess the coverage of endpoints in E2E testing. Metric extraction process and proof-of-concept tool imlementation.
Though various metrics exist for each phase of software life cycle but substantial work is needed in testing phase in particular. This paper surveys and classifies various testing metrics. It also proposes some new software product testing metrics. The proposed metrics are analyzed over project data given by NASA[1].Planning information security investment is somewhere between art and science. This paper reviews and compares existing scientific approaches and discusses the relation between security investment models and security metrics. To structure the exposition, the.
measuring corneal thickness
2.1 Risk Management. The Information Security Management Systems (ISMS) is a concept introduced in the security standard ISO/IEC 27000 and promotes a model to establish, implement, operate, monitor, review, maintain and improve the protection of information assets, which has value and requires adequate protection against the loss of the information security . Testing is the evaluation of software by observing its execution [].The executed system is called system under test (SUT). Testing consists of the dynamic verification of the behavior of a system on a finite set of test cases, a so called test suite, suitably selected from the usually infinite set of execution traces, against the expected behavior [].In this article we only .
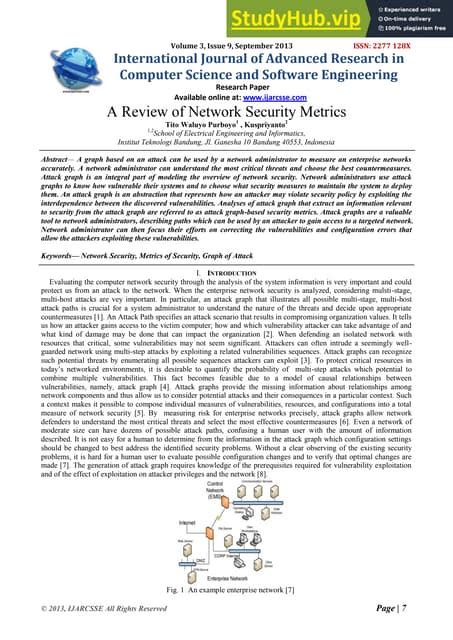
The security metrics proposed in this paper hold immense promise for advancing network security evaluation. . One possible avenue of future work would involve generation of synthetic attack graphs to test the efficacy of the proposed security metrics. . Jajodia, S., Singhal, A. (eds.) Network Security Metrics, pp. 1–23. Springer, Cham . In Sect. 1, we mentioned that fuzzing is performed by generating and sending potentially malformed data to an application.Nowadays, fuzzing is used for testing different types of input interfaces such as: network protocols [], file formats [], in-memory fuzzing [], drivers and many others software and hardware products that process input data.. Moreover, fuzzing is . Recent studies have shown that modern deep neural network classifiers are easy to fool, assuming that an adversary is able to slightly modify their inputs. Many papers have proposed adversarial attacks, defenses and methods to measure robustness to such adversarial perturbations. However, most commonly considered adversarial examples are based on . 2.1 Cyber Security Metrics. According to National Institute of Standards and Technology (NIST) [], “metrics are tools that are designed to facilitate decision-making and improve performance and accountability through collection, analysis, and reporting of relevant performance-related data”.A metric can be developed to measure cyber security trust .
A method traditionally used to measure the usability level of software products is the well-known usability testing. In this method, people are employed as participants and usability experts commonly use usability metrics to be able to evaluate participants as they interact with the software product from which they want to measure their level of usability. All Internet facing systems and applications carry security risks. Security professionals across the globe generally address these security risks by Vulnerability Assessment and Penetration Testing (VAPT). The VAPT is an offensive way of defending the cyber assets of an organization. It consists of two major parts, namely Vulnerability .
security metrics review pdf
measuring corneal thickness with oct
measuring cortical thickness zebrafish
measuring cr thickness
measuring cr3 thickness
webInvestingHaven.com. “The price of silver will move to our first bullish target in 2024 which is $34.70. We predict $48 to be hit either by mid-2024 or mid-2025.”. JP Morgan. “The Fed cutting cycle and falling U.S. real yields are expected to push gold prices to new nominal highs in the middle of 2024, reaching an average of $2,175/oz by .
springer white papers on security testing metrics|security metrics review pdf